ZIP: 32
Title: Shielded Hierarchical Deterministic Wallets
Owners: Jack Grigg <[email protected]>
Daira-Emma Hopwood <[email protected]>
Credits: Sean Bowe
Kris Nuttycombe
Ying Tong Lai
Pieter Wuille
Marek Palatinus
Pavol Rusnak
Status: Final
Category: Standards / Wallet
Created: 2018-05-22
License: MIT
\(% This ZIP makes heavy use of mathematical markup. If you can see this, you may want to instead view the rendered version at https://zips.z.cash/zip-0032 .\)
Terminology 
The key words "MUST", "MUST NOT", "SHOULD", "RECOMMENDED", and "MAY" in this document are to be interpreted as described in BCP 14 1 when, and only when, they appear in all capitals.
"Jubjub" refers to the elliptic curve defined in 15.
A "cryptovalue" is a high-entropy value used in a cryptographic protocol that is not necessarily a key.
A "chain code" is a cryptovalue that is needed, in addition to a spending key, in order to derive descendant keys and addresses of that key.
The terms "Testnet" and "Mainnet" are to be interpreted as described in section 3.12 of the Zcash Protocol Specification 10.
Abstract 
This proposal defines a mechanism for extending hierarchical deterministic wallets, as described in BIP 32 2, to support Zcash's shielded addresses.
The initial parts of the specification define (mostly) equivalent, but independent, systems for deriving a tree of key components from a single seed, for the following shielded pools (which have different internal key structures):
- Sapling
- Orchard
Previous versions of this document also defined a similar derivation system for the Sprout shielded pool. This has been removed since it was never used, and is unlikely to be used given that zcashd no longer generates Sprout addresses (and neither Zebra nor the mobile SDKs have ever done so).
The last part shows how to use these trees in the context of existing BIP 44 6 wallets.
This specification complements the existing use by some Zcash wallets of BIP 32 and BIP 44 for transparent Zcash addresses, and is not intended to deprecate that usage (privacy risks of using transparent addresses notwithstanding).
Motivation 
BIP 32 2 is the standard mechanism by which wallets for Bitcoin and its derivatives (including Zcash's transparent addresses 7) generate keys and addresses deterministically. This has several advantages over random generation:
- Wallets only need to store a single seed (particularly useful for hardware wallets).
- A one-time backup of the seed (usually stored as a BIP 39 mnemonic 3 or SLIP 39 shares 4) can be used to recover funds from all future addresses.
- Keys are arranged into a tree of chains, enabling wallets to represent "accounts" or other high-level structures.
- Viewing authority or spending authority can be delegated independently for sub-trees without compromising the master seed.
At present, no such equivalent exists for Zcash's shielded addresses. This is of particular concern for hardware wallets; all currently-marketed devices only store a seed internally, and have trained their users to only backup that seed. Given that the Sapling upgrade will make it feasible to use hardware wallets with shielded addresses, it is desirable to have a standard mechanism for deriving them.
Conventions 
Most of the notation and functions used in this ZIP are defined in the Zcash protocol specification 9. They are reproduced here for convenience:
- \(\mathsf{truncate}_k(S)\) means the sequence formed from the first \(k\) elements of \(S\!\) .
- \(a\,||\,b\) means the concatenation of sequences \(a\) then \(b\!\) .
- \([k] P\) means scalar multiplication of the elliptic curve point \(P\) by the scalar \(k\!\) .
- \(\mathsf{LEOS2IP}_\ell(S)\) is the integer in range \(\{ 0\,..\, 2^\ell - 1 \}\) represented in little-endian order by the byte sequence \(S\) of length \(\ell/8\!\) .
- \(\mathsf{I2LEBSP}_\ell(k)\) is the sequence of \(\ell\) bits representing \(k\) in little-endian order.
- \(\mathsf{LEBS2OSP}_\ell(B)\) is defined as follows when \(\ell\) is a multiple of \(8\!\) : convert each group of 8 bits in \(B\) to a byte value with the least significant bit first, and concatenate the resulting bytes in the same order as the groups.
- \(\mathsf{repr}_\mathbb{J}(P)\) is the representation of the Jubjub elliptic curve point \(P\) as a bit sequence, defined in 15.
- \(\mathsf{BLAKE2b}\text{-}\mathsf{256}(p, x)\) refers to unkeyed BLAKE2b-256 in sequential mode, with an output digest length of 32 bytes, 16-byte personalization string \(p\!\) , and input \(x\!\) .
- \(\mathsf{BLAKE2b}\text{-}\mathsf{512}(p, x)\) refers to unkeyed BLAKE2b-512 in sequential mode, with an output digest length of 64 bytes, 16-byte personalization string \(p\!\) , and input \(x\!\) .
- \(\mathsf{PRF^{expand}}(\mathsf{sk}, t) :=\) \(\mathsf{BLAKE2b}\text{-}\mathsf{512}(\texttt{“Zcash\_ExpandSeed”},\) \(\mathsf{sk}\,||\,t)\!\) .
- \(r_\mathbb{J}\) is the order of the Jubjub large prime subgroup.
- \(r_\mathbb{P}\) is the order of the Pallas curve.
- \(\mathsf{ToScalar^{Sapling}}(x) :=\) \(\mathsf{LEOS2IP}_{512}(x) \pmod{r_\mathbb{J}}\!\) .
- \(\mathsf{ToScalar^{Orchard}}(x) :=\) \(\mathsf{LEOS2IP}_{512}(x) \pmod{r_\mathbb{P}}\!\) .
- \(\mathsf{DiversifyHash^{Sapling}}(d)\) maps a diversifier \(d\) to a base point on the Jubjub elliptic curve, or to \(\bot\) if the diversifier is invalid. It is instantiated in 13.
The following algorithm standardized in 22 is used:
- \(\mathsf{FF1}\text{-}\mathsf{AES256.Encrypt}(key, tweak, x)\) refers to the FF1 encryption algorithm using AES with a 256-bit \(key\!\) , and parameters \(radix = 2,\) \(minlen = 88,\) \(maxlen = 88\!\) . It will be used only with the empty string \(\texttt{“”}\) as the \(tweak\!\) . \(x\) is a sequence of 88 bits, as is the output.
We also define the following conversion function:
- \(\mathsf{I2LEOSP}_\ell(k)\) is the byte sequence \(S\) of length \(\ell/8\) representing in little-endian order the integer \(k\) in range \(\{ 0\,..\, 2^\ell - 1 \}\!\) . It is the reverse operation of \(\mathsf{LEOS2IP}_\ell(S)\!\) .
Implementors should note that this ZIP is consistently little-endian (in keeping with the Sapling and Orchard specifications), which is the opposite of BIP 32.
We adapt the path notation of BIP 32 2 to describe shielded HD paths, using prime marks ( \(\kern-0.1em{}'\!\) ) to indicate hardened derivation ( \(\!i' = i + 2^{31}\!\) ) as in BIP 44 6:
- \(\mathsf{CKDfvk}(\mathsf{CKDfvk}(\mathsf{CKDfvk}(m_\mathsf{Sapling}, a), b), c)\) is written as \(m_\mathsf{Sapling} / a / b / c\!\) .
Note: no corresponding notation is currently defined for the result of Hardened-only child key derivation with non-zero \(\mathsf{lead}\) and/or non-empty \(\mathsf{tag}\!\) .
Specification: Wallet seeds 
Several of the key derivation algorithms specified in this ZIP derive a master key from a seed byte sequence. Any such seed byte sequence MUST be at least 32 and at most 252 bytes.
The method of generating such a seed byte sequence for Zcash purposes MUST ensure that it has at least 256 bits of entropy. This requirement also applies to any mnemonic or input randomness used to obtain the seed byte sequence. See ZIP 315 27 for further guidance.
Rationale for the 256-bit entropy requirement 
Click to show/hide
Zcash consistently uses cryptovalues of length at or close to 256 bits, throughout its cryptographic design. Although the target security level for the protocol against classical cryptanalytic attacks is \(2^{125}\) (i.e. any such attack should take at least \(2^{125}\) operations, as explained in 23), this does not imply that 128-bit keys or seeds are sufficient. The apparent gap between the security target and the key length is well motivated: it provides better resistance to attacks using parallel hardware 24 in the multi-user setting 25; it takes into account small entropy losses in the key derivation process; and it simplifies the analysis of the protocol against quantum attacks for unknown addresses 23, or in the context of a future post-quantum recovery protocol 29.
In particular, for the hierarchical key derivation method described in this ZIP, if the seed or mnemonic has entropy less than 256 bits, it will be a weak link in the derivation of all keys belonging to that wallet.
It should be noted that an adversary can search for uses of lower-entropy mnemonics across multiple wallets simultaneously. They can collect a large set of (transparent or shielded) target addresses and/or viewing keys, and then perform a brute-force search over mnemonics in a lower-entropy subspace, efficiently checking whether the first few addresses or viewing keys that would be generated from each mnemonic match any of the targets.
Specification: Sapling key derivation 
Sapling extended keys 
BIP 32 defines a method to derive a number of child keys from a parent key. In order to prevent these from depending solely on the parent key itself, both the private and public keys are extended with a 32-byte chain code. We similarly extend Sapling keys with a chain code here. However, the concepts of "private" and "public" keys in BIP 32 do not map cleanly to Sapling's key components. We take the following approach:
- We derive child Sapling expanded spending keys, rather than Sapling spending keys. This enables us to implement both hardened and non-hardened derivation modes (the latter being incompatible with Sapling spending keys).
- We do not derive Sapling public keys directly, as this would prevent the use of diversified addresses. Instead, we derive Sapling full viewing keys, from which payment addresses can be generated. This maintains the trust semantics of BIP 32: someone with access to a BIP 32 extended public key is able to view all transactions involving that address, which a Sapling full viewing key also enables.
We represent a Sapling extended spending key as \((\mathsf{ask, nsk, ovk, dk, c})\!\) , where \((\mathsf{ask, nsk, ovk})\) is the normal Sapling expanded spending key, \(\mathsf{dk}\) is a diversifier key, and \(\mathsf{c}\) is the chain code.
We represent a Sapling extended full viewing key as \((\mathsf{ak, nk, ovk, dk, c})\!\) , where \((\mathsf{ak, nk, ovk})\) is the normal Sapling full viewing key, \(\mathsf{dk}\) is the same diversifier key as above, and \(\mathsf{c}\) is the chain code.
Sapling helper functions 
Define
- \(\mathsf{EncodeExtSKParts}(\mathsf{ask, nsk, ovk, dk}) :=\) \(\mathsf{I2LEOSP}_{256}(\mathsf{ask})\) \(||\,\mathsf{I2LEOSP}_{256}(\mathsf{nsk})\) \(||\,\mathsf{ovk}\) \(||\,\mathsf{dk}\)
- \(\mathsf{EncodeExtFVKParts}(\mathsf{ak, nk, ovk, dk}) :=\) \(\mathsf{LEBS2OSP}_{256}(\mathsf{repr}_\mathbb{J}(\mathsf{ak}))\) \(||\,\mathsf{LEBS2OSP}_{256}(\mathsf{repr}_\mathbb{J}(\mathsf{nk}))\) \(||\,\mathsf{ovk}\) \(||\,\mathsf{dk}\)
Sapling master key generation 
Let \(S\) be a seed byte sequence meeting the requirements in Specification: Wallet seeds.
- Calculate \(I = \mathsf{BLAKE2b}\text{-}\mathsf{512}(\texttt{“ZcashIP32Sapling”}, S)\!\) .
- Split \(I\) into two 32-byte sequences, \(I_L\) and \(I_R\!\) .
- Use \(I_L\) as the master spending key \(\mathsf{sk}_m\!\) , and \(I_R\) as the master chain code \(\mathsf{c}_m\!\) .
- Calculate
\(\mathsf{ask}_m\!\)
,
\(\mathsf{nsk}_m\!\)
, and
\(\mathsf{ovk}_m\)
via the standard Sapling derivation 11:
- \(\mathsf{ask}_m = \mathsf{ToScalar^{Sapling}}(\mathsf{PRF^{expand}}(\mathsf{sk}_m, [\mathtt{0x00}]))\)
- \(\mathsf{nsk}_m = \mathsf{ToScalar^{Sapling}}(\mathsf{PRF^{expand}}(\mathsf{sk}_m, [\mathtt{0x01}]))\)
- \(\mathsf{ovk}_m = \mathsf{truncate}_{32}(\mathsf{PRF^{expand}}(\mathsf{sk}_m, [\mathtt{0x02}]))\!\) .
- Calculate
\(\mathsf{dk}_m\)
similarly:
- \(\mathsf{dk}_m = \mathsf{truncate}_{32}(\mathsf{PRF^{expand}}(\mathsf{sk}_m, [\mathtt{0x10}]))\!\) .
- Return \((\mathsf{ask}_m, \mathsf{nsk}_m, \mathsf{ovk}_m, \mathsf{dk}_m, \mathsf{c}_m)\) as the master extended spending key \(m_\mathsf{Sapling}\!\) .
Note that the master extended key is invalid if \(\mathsf{ask}_m\) is \(0\!\) , or if the corresponding \(\mathsf{ivk}\) derived as specified in 11 is \(0\!\) .
Sapling child key derivation 
As in BIP 32, the method for deriving a child extended key, given a parent extended key and an index \(i\!\) , depends on the type of key being derived, and whether this is a hardened or non-hardened derivation.
Deriving a child extended spending key 
\(\mathsf{CKDsk}((\mathsf{ask}_{par}, \mathsf{nsk}_{par}, \mathsf{ovk}_{par}, \mathsf{dk}_{par}, \mathsf{c}_{par}), i)\) \(\rightarrow (\mathsf{ask}_i, \mathsf{nsk}_i, \mathsf{ovk}_i, \mathsf{dk}_i, \mathsf{c}_i)\) :
- Check whether
\(i \geq 2^{31}\)
(whether the child is a hardened key).
- If so (hardened child): let \(I = \mathsf{PRF^{expand}}(\mathsf{c}_{par}, [\mathtt{0x11}]\) \(||\,\mathsf{EncodeExtSKParts}(\mathsf{ask}_{par}, \mathsf{nsk}_{par}, \mathsf{ovk}_{par}, \mathsf{dk}_{par})\) \(||\,\mathsf{I2LEOSP}_{32}(i))\!\) .
- If not (normal child): let \(I = \mathsf{PRF^{expand}}(\mathsf{c}_{par}, [\mathtt{0x12}]\) \(||\,\mathsf{EncodeExtFVKParts}(\mathsf{ak}_{par}, \mathsf{nk}_{par}, \mathsf{ovk}_{par}, \mathsf{dk}_{par})\) \(||\,\mathsf{I2LEOSP}_{32}(i))\) where \((\mathsf{nk}_{par}, \mathsf{ak}_{par}, \mathsf{ovk}_{par})\) is the full viewing key derived from \((\mathsf{ask}_{par}, \mathsf{nsk}_{par}, \mathsf{ovk}_{par})\) as described in 11.
- Split \(I\) into two 32-byte sequences, \(I_L\) and \(I_R\!\) .
- Let \(I_\mathsf{ask} = \mathsf{ToScalar^{Sapling}}(\mathsf{PRF^{expand}}(I_L, [\mathtt{0x13}]))\!\) .
- Let \(I_\mathsf{nsk} = \mathsf{ToScalar^{Sapling}}(\mathsf{PRF^{expand}}(I_L, [\mathtt{0x14}]))\!\) .
- Return:
- \(\mathsf{ask}_i = (I_\mathsf{ask} + \mathsf{ask}_{par}) \pmod{r_\mathbb{J}}\)
- \(\mathsf{nsk}_i = (I_\mathsf{nsk} + \mathsf{nsk}_{par}) \pmod{r_\mathbb{J}}\)
- \(\mathsf{ovk}_i = \mathsf{truncate}_{32}(\mathsf{PRF^{expand}}(I_L, [\mathtt{0x15}]\) \(||\,\mathsf{ovk}_{par}))\)
- \(\mathsf{dk}_i = \mathsf{truncate}_{32}(\mathsf{PRF^{expand}}(I_L, [\mathtt{0x16}]\) \(||\,\mathsf{dk}_{par}))\)
- \(\mathsf{c}_i = I_R\!\) .
Note that the child extended key is invalid if \(\mathsf{ask}_i\) is \(0\!\) , or if the corresponding \(\mathsf{ivk}\) derived as specified in 11 is \(0\!\) .
Deriving a child extended full viewing key 
Let \(\mathcal{G}^\mathsf{Sapling}\) be as defined in 14 and let \(\mathcal{H}^\mathsf{Sapling}\) be as defined in 11.
\(\mathsf{CKDfvk}((\mathsf{ak}_{par}, \mathsf{nk}_{par}, \mathsf{ovk}_{par}, \mathsf{dk}_{par}, \mathsf{c}_{par}), i)\) \(\rightarrow (\mathsf{ak}_{i}, \mathsf{nk}_{i}, \mathsf{ovk}_{i}, \mathsf{dk}_{i}, \mathsf{c}_{i})\) :
- Check whether
\(i \geq 2^{31}\)
(whether the child is a hardened key).
- If so (hardened child): return failure.
- If not (normal child): let \(I = \mathsf{PRF^{expand}}(\mathsf{c}_{par}, [\mathtt{0x12}]\) \(||\,\mathsf{EncodeExtFVKParts}(\mathsf{ak}_{par}, \mathsf{nk}_{par}, \mathsf{ovk}_{par}, \mathsf{dk}_{par})\) \(||\,\mathsf{I2LEOSP}_{32}(i))\!\) .
- Split \(I\) into two 32-byte sequences, \(I_L\) and \(I_R\!\) .
- Let \(I_\mathsf{ask} = \mathsf{ToScalar^{Sapling}}(\mathsf{PRF^{expand}}(I_L, [\mathtt{0x13}]))\!\) .
- Let \(I_\mathsf{nsk} = \mathsf{ToScalar^{Sapling}}(\mathsf{PRF^{expand}}(I_L, [\mathtt{0x14}]))\!\) .
- Return:
- \(\mathsf{ak}_i = [I_\mathsf{ask}]\,\mathcal{G}^\mathsf{Sapling} + \mathsf{ak}_{par}\)
- \(\mathsf{nk}_i = [I_\mathsf{nsk}]\,\mathcal{H}^\mathsf{Sapling} + \mathsf{nk}_{par}\)
- \(\mathsf{ovk}_i = \mathsf{truncate}_{32}(\mathsf{PRF^{expand}}(I_L, [\mathtt{0x15}]\) \(||\,\mathsf{ovk}_{par}))\)
- \(\mathsf{dk}_i = \mathsf{truncate}_{32}(\mathsf{PRF^{expand}}(I_L, [\mathtt{0x16}]\) \(||\,\mathsf{dk}_{par}))\)
- \(\mathsf{c}_i = I_R\!\) .
Note that the child extended key is invalid if \(\mathsf{ak}_i\) is the zero point of Jubjub, or if the corresponding \(\mathsf{ivk}\) derived as specified in 11 is \(0\!\) .
Sapling internal key derivation 
The above derivation mechanisms produce external addresses suitable for giving out to senders. We also want to be able to produce another address derived from a given external address, for use by wallets for internal operations such as change and auto-shielding. Unlike BIP 44 that allows deriving a stream of external and internal addresses in the same hierarchical derivation tree 6, for any external full viewing key we only need to be able to derive a single internal full viewing key that has viewing authority for just internal transfers. We also need to be able to derive the corresponding internal spending key if we have the external spending key.
Deriving a Sapling internal spending key 
Let \((\mathsf{ask}, \mathsf{nsk}, \mathsf{ovk}, \mathsf{dk})\) be the external spending key.
- Derive the corresponding \(\mathsf{ak}\) and \(\mathsf{nk}\) as specified in 11.
- Let \(I = \textsf{BLAKE2b-256}(\texttt{“Zcash\_SaplingInt”}, \mathsf{EncodeExtFVKParts}(\mathsf{ak}, \mathsf{nk}, \mathsf{ovk}, \mathsf{dk}))\!\) .
- Let \(I_\mathsf{nsk} = \mathsf{ToScalar^{Sapling}}(\mathsf{PRF^{expand}}(I, [\mathtt{0x17}]))\!\) .
- Let \(R = \mathsf{PRF^{expand}}(I, [\mathtt{0x18}])\!\) .
- Let \(\mathsf{nsk_{internal}} = (I_\mathsf{nsk} + \mathsf{nsk}) \pmod{r_\mathbb{J}}\!\) .
- Split \(R\) into two 32-byte sequences, \(\mathsf{dk_{internal}}\) and \(\mathsf{ovk_{internal}}\!\) .
- Return the internal spending key as \((\mathsf{ask}, \mathsf{nsk_{internal}}, \mathsf{ovk_{internal}}, \mathsf{dk_{internal}})\!\) .
Note that the child extended key is invalid if \(\mathsf{ak}\) is the zero point of Jubjub, or if the corresponding \(\mathsf{ivk}\) derived as specified in 11 is \(0\!\) .
Deriving a Sapling internal full viewing key 
Let \(\mathcal{H}^\mathsf{Sapling}\) be as defined in 11.
Let \((\mathsf{ak}, \mathsf{nk}, \mathsf{ovk}, \mathsf{dk})\) be the external full viewing key.
- Let \(I = \textsf{BLAKE2b-256}(\texttt{“Zcash\_SaplingInt”}, \mathsf{EncodeExtFVKParts}(\mathsf{ak}, \mathsf{nk}, \mathsf{ovk}, \mathsf{dk}))\!\) .
- Let \(I_\mathsf{nsk} = \mathsf{ToScalar^{Sapling}}(\mathsf{PRF^{expand}}(I, [\mathtt{0x17}]))\!\) .
- Let \(R = \mathsf{PRF^{expand}}(I, [\mathtt{0x18}])\!\) .
- Let \(\mathsf{nk_{internal}} = [I_\mathsf{nsk}] \mathcal{H}^\mathsf{Sapling} + \mathsf{nk}\!\) .
- Split \(R\) into two 32-byte sequences, \(\mathsf{dk_{internal}}\) and \(\mathsf{ovk_{internal}}\!\) .
- Return the internal full viewing key as \((\mathsf{ak}, \mathsf{nk_{internal}}, \mathsf{ovk_{internal}}, \mathsf{dk_{internal}})\!\) .
This design uses the same technique as non-hardened derivation to obtain a full viewing key with the same spend authority (the private key corresponding to \(\mathsf{ak}\!\) ) as the original, but viewing authority only for internal transfers.
The values of \(I\!\) , \(I_\mathsf{nsk}\!\) , and \(R\) are the same between deriving a full viewing key, and deriving the corresponding spending key. Both of these derivations are shown in the following diagram:
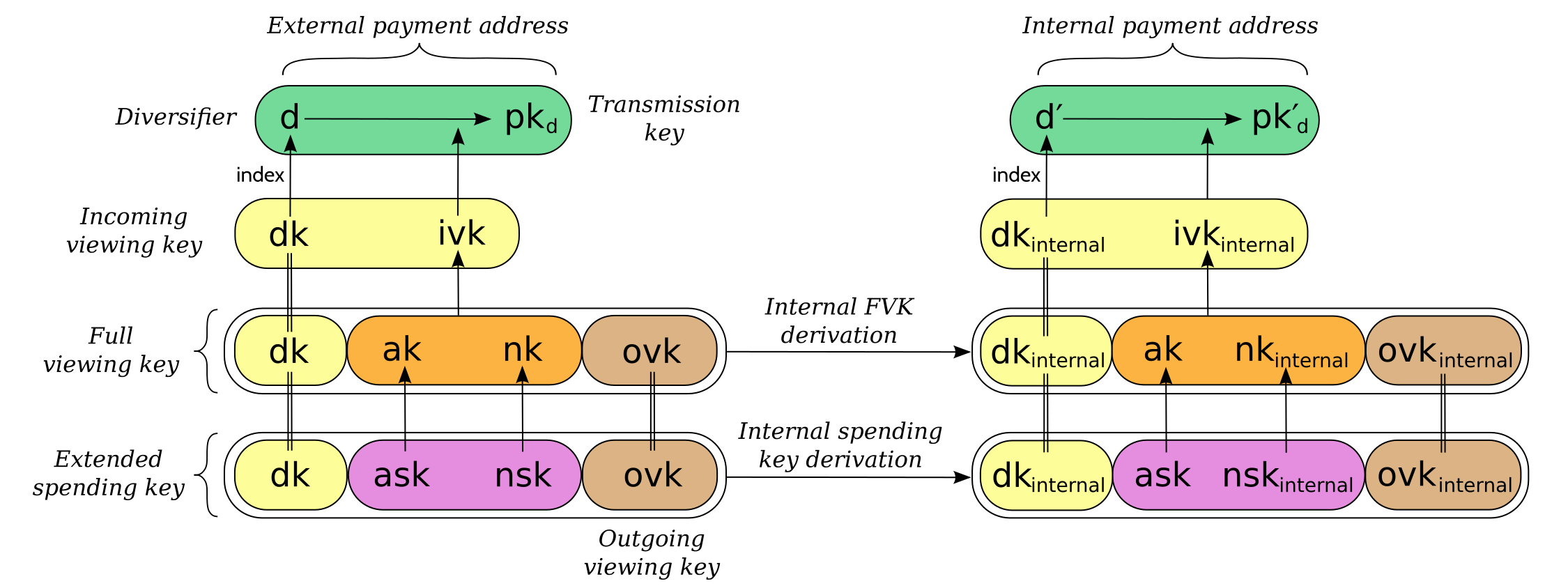
(For simplicity, the proof authorizing key is not shown.)
This method of deriving internal keys is applied to external keys that are children of the Account level. It was implemented in zcashd as part of support for ZIP 316 28.
Note that the internal extended key is invalid if \(\mathsf{ak}\) is the zero point of Jubjub, or if the corresponding \(\mathsf{ivk_{internal}}\) derived from the internal full viewing key as specified in 11 is \(0\!\) .
Sapling diversifier derivation 
The 88-bit diversifiers for a Sapling extended key are derived from its diversifier key \(\mathsf{dk}\!\) . To prevent the diversifier leaking how many diversified addresses have already been generated for an account, we make the sequence of diversifiers pseudorandom and uncorrelated to that of any other account. In order to reach the maximum possible diversifier range without running into repetitions due to the birthday bound, we use FF1-AES256 as a Pseudo-Random Permutation as follows:
- Let \(j\) be the index of the desired diversifier, in the range \(0\,..\, 2^{88} - 1\!\) .
- \(d_j = \mathsf{FF1}\text{-}\mathsf{AES256.Encrypt}(\mathsf{dk}, \texttt{“”}, \mathsf{I2LEBSP}_{88}(j))\!\) .
A valid diversifier \(d_j\) is one for which \(\mathsf{DiversifyHash^{Sapling}}(d_j) \neq \bot\!\) . For a given \(\mathsf{dk}\!\) , approximately half of the possible values of \(j\) yield valid diversifiers.
The default diversifier for a Sapling extended key is defined to be \(d_j\!\) , where \(j\) is the least nonnegative integer yielding a valid diversifier.
Specification: Hardened-only key derivation 
The derivation mechanism for Sapling addresses specified above incurs significant complexity to support non-hardened derivation. In the several years since Sapling was deployed, we have seen no use cases for non-hardened derivation appear. With that in mind, we now have a general hardened-only derivation process that retains compatibility with existing derivation path semantics (to enable deriving the same path across multiple contexts).
The functions defined in this section are intended for internal use by context-specific mechanisms in subsequent sections, rather than for direct use.
Instantiation 
Let \(\mathsf{Context}\) be the context in which the hardened-only key derivation process is instantiated (e.g. a shielded protocol). We define two context-specific constants:
- \(\mathsf{Context.MKGDomain}\) is a sequence of 16 bytes, used as a domain separator during master key generation. It SHOULD be disjoint from other domain separators used with BLAKE2b in Zcash protocols.
- \(\mathsf{Context.CKDDomain}\) is a byte value, used as a domain separator during child key derivation. This should be tracked as part of the global set of domains defined for \(\mathsf{PRF^{expand}}\!\) .
Hardened-only master key generation 
Let \(\mathsf{IKM}\) be an input key material byte sequence, which MUST use an unambiguous encoding within the given context, and SHOULD contain at least 256 bits of entropy. It is RECOMMENDED to use a prefix-free encoding, which may require the use of length fields if multiple fields need to be encoded.
\(\mathsf{MKGh}^\mathsf{Context}(\mathsf{IKM}) \rightarrow (\mathsf{sk}_m, \mathsf{c}_m)\) :
- Calculate \(I = \mathsf{BLAKE2b}\text{-}\mathsf{512}(\mathsf{Context.MKGDomain}, \mathsf{IKM})\!\) .
- Split \(I\) into two 32-byte sequences, \(I_L\) and \(I_R\!\) .
- Use \(I_L\) as the master secret key \(\mathsf{sk}_m\!\) .
- Use \(I_R\) as the master chain code \(\mathsf{c}_m\!\) .
- Return \((\mathsf{sk}_m, \mathsf{c}_m)\!\) .
Hardened-only child key derivation 
As well as the integer child index \(i\!\) , the child key derivation function defined here supports a lead byte \(\mathsf{lead}\) (used for domain separation) and byte sequence \(\mathsf{tag}\!\) . Each triple \((i, \mathsf{lead}, \mathsf{tag})\) produces an independent output.
\(\mathsf{CKDh}^\mathsf{Context}((\mathsf{sk}_{par}, \mathsf{c}_{par}), i, \mathsf{lead}, \mathsf{tag})\) \(\rightarrow (\mathsf{sk}_{child}, \mathsf{c}_{child})\) :
- If \(i < 2^{31}\) (non-hardened child index): return failure.
- Let \(\mathsf{lead\_enc} = \begin{cases} \,[\,],&\!\!\textsf{if } \mathsf{lead} = 0 \textsf{ and } \mathsf{tag} = [\,] \\ \,[\mathsf{lead}],&\!\!\textsf{otherwise.}\end{cases}\)
- Let \(I = \mathsf{PRF^{expand}}(\mathsf{c}_{par}, [\mathsf{Context.CKDDomain}]\,||\,\mathsf{sk}_{par}\,||\,\mathsf{I2LEOSP}_{32}(i)\,||\,\mathsf{lead\_enc}\,||\,\mathsf{tag})\!\) .
- Split \(I\) into two 32-byte sequences, \(I_L\) and \(I_R\!\) .
- Return \((I_L, I_R)\!\) .
Note that in the input to \(\mathsf{PRF^{expand}}\!\) , the case \(\mathsf{lead} = 0\) and \(\mathsf{tag} = [\,]\) is encoded in a way compatible with the definition of \(\mathsf{CKDh}\) in previous versions of this specification (before \(\mathsf{lead}\) and \(\mathsf{tag}\) were added).
Specification: Orchard key derivation 
We only support hardened key derivation for Orchard. We instantiate the hardened key generation process with the following constants:
- \(\mathsf{Orchard.MKGDomain} = \texttt{“ZcashIP32Orchard”}\)
- \(\mathsf{Orchard.CKDDomain} = \mathtt{0x81}\)
Orchard extended keys 
We represent an Orchard extended spending key as \((\mathsf{sk, c}),\) where \(\mathsf{sk}\) is the normal Orchard spending key (opaque 32 bytes), and \(\mathsf{c}\) is the chain code.
Orchard master key generation 
Let \(S\) be a seed byte sequence meeting the requirements in Specification: Wallet seeds.
- Return \(\mathsf{MKGh}^\mathsf{Orchard}(S)\) as the master extended spending key \(m_\mathsf{Orchard}\!\) .
Orchard child key derivation 
\(\mathsf{CKDsk}((\mathsf{sk}_{par}, \mathsf{c}_{par}), i)\) \(\rightarrow (\mathsf{sk}_{i}, \mathsf{c}_i)\) :
- Return \(\mathsf{CKDh}^\mathsf{Orchard}((\mathsf{sk}_{par}, \mathsf{c}_{par}), i, 0, [\,])\)
Note that the resulting child spending key may produce an invalid external FVK, as specified in 12, with small probability. The corresponding internal FVK derived as specified in the next section may also be invalid with small probability.
Orchard internal key derivation 
As in the case of Sapling, for a given external address, we want to produce another address for use by wallets for internal operations such as change and auto-shielding. That is, for any external full viewing key we need to be able to derive a single internal full viewing key that has viewing authority for just internal transfers. We also need to be able to derive the corresponding internal spending key if we have the external spending key.
Let \(\mathsf{ask}\) be the spend authorizing key if available, and let \((\mathsf{ak}, \mathsf{nk}, \mathsf{rivk})\) be the corresponding external full viewing key, obtained as specified in 12.
Define \(\mathsf{DeriveInternalFVK^{Orchard}}(\mathsf{ak}, \mathsf{nk}, \mathsf{rivk})\) as follows:
- Let \(K = \mathsf{I2LEBSP}_{256}(\mathsf{rivk})\!\) .
- Let \(\mathsf{rivk_{internal}} = \mathsf{ToScalar^{Orchard}}(\mathsf{PRF^{expand}}(K, [\mathtt{0x83}] \,||\, \mathsf{I2LEOSP_{256}}(\mathsf{ak}) \,||\, \mathsf{I2LEOSP_{256}}(\mathsf{nk})))\!\) .
- Return \((\mathsf{ak}, \mathsf{nk}, \mathsf{rivk_{internal}})\!\) .
The result of applying \(\mathsf{DeriveInternalFVK^{Orchard}}\) to the external full viewing key is the internal full viewing key. The corresponding expanded internal spending key is \((\mathsf{ask}, \mathsf{nk}, \mathsf{rivk_{internal}})\!\) .
Unlike Sapling internal key derivation, we do not base this internal key derivation procedure on non-hardened derivation, which is not defined for Orchard. We can obtain the desired separation of viewing authority by modifying only the \(\mathsf{rivk_{internal}}\) field relative to the external full viewing key, which results in different \(\mathsf{dk_{internal}}\!\) , \(\mathsf{ivk_{internal}}\) and \(\mathsf{ovk_{internal}}\) fields being derived, as specified in 12 and shown in the following diagram:
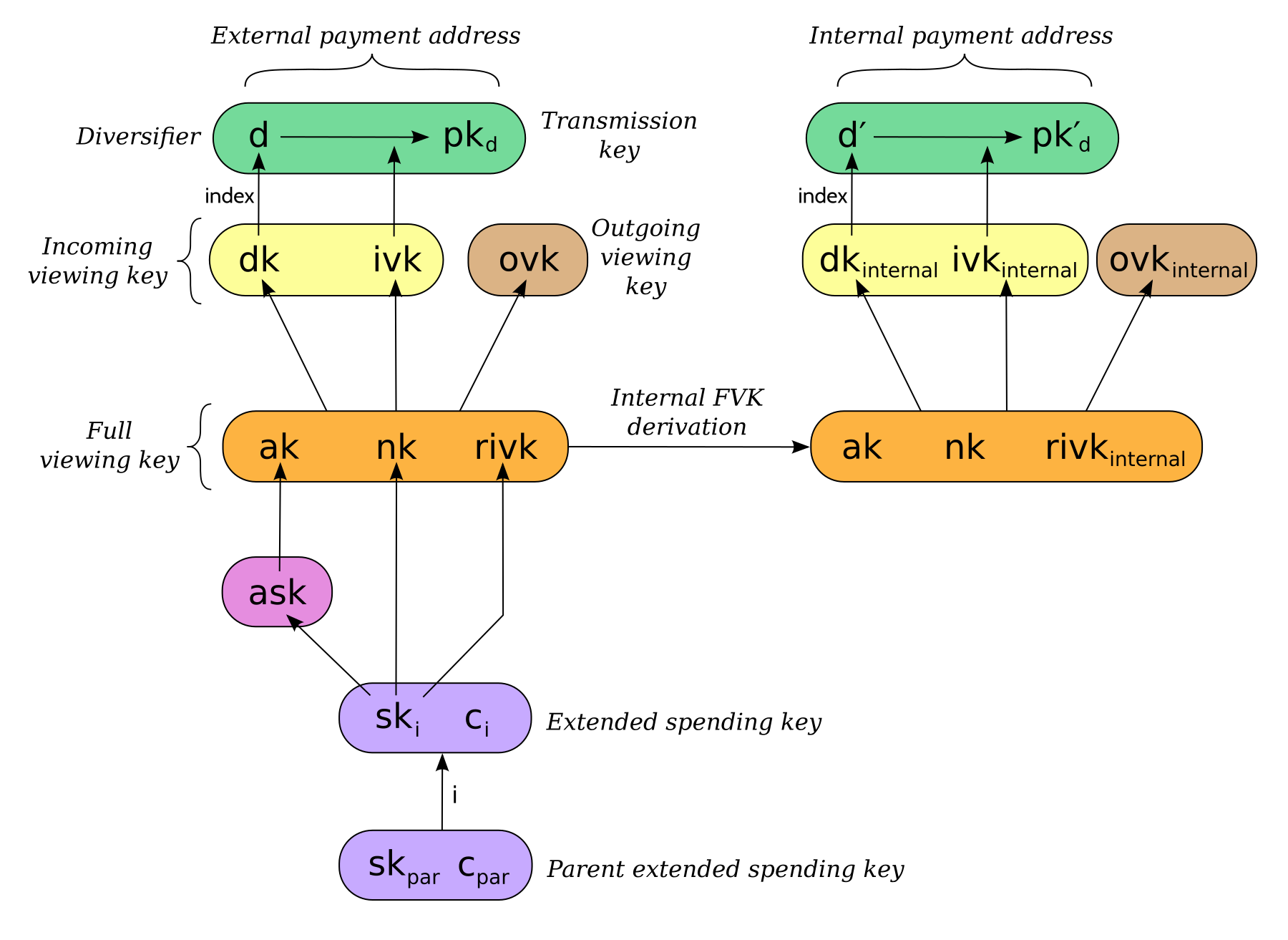
This method of deriving internal keys is applied to external keys that are children of the Account level. It was implemented in zcashd as part of support for ZIP 316 28.
Note that the resulting FVK may be invalid, as specified in 12.
Orchard diversifier derivation 
As with Sapling, we define a mechanism for deterministically deriving a sequence of diversifiers, without leaking how many diversified addresses have already been generated for an account. Unlike Sapling, we do so by deriving a diversifier key directly from the full viewing key, instead of as part of the extended spending key. This means that the full viewing key provides the capability to determine the position of a diversifier within the sequence, which matches the capabilities of a Sapling extended full viewing key but simplifies the key structure.
Given an Orchard extended spending key \((\mathsf{sk}_i, \mathsf{c}_i)\!\) :
- Let \((\mathsf{ak}, \mathsf{nk}, \mathsf{rivk})\) be the Orchard full viewing key for \(\mathsf{sk}_i\!\) .
- Let \(K = \mathsf{I2LEBSP}_{256}(\mathsf{rivk})\!\) .
- \(\mathsf{dk}_i = \mathsf{truncate}_{32}(\mathsf{PRF^{expand}}(K, [\mathtt{0x82}] \,||\, \mathsf{I2LEOSP}_{256}(\mathsf{ak}) \,||\, \mathsf{I2LEOSP}_{256}(\mathsf{nk})))\!\) .
- Let \(j\) be the index of the desired diversifier, in the range \(0\,..\, 2^{88} - 1\!\) .
- \(d_{i,j} = \mathsf{FF1}\text{-}\mathsf{AES256.Encrypt}(\mathsf{dk}_i, \texttt{“”}, \mathsf{I2LEBSP}_{88}(j))\!\) .
Note that unlike Sapling, all Orchard diversifiers are valid, and thus all possible values of \(j\) yield valid diversifiers.
The default diversifier for \((\mathsf{sk}_i, \mathsf{c}_i)\) is defined to be \(d_{i,0}.\)
Specification: Registered key derivation 
In the context of a particular application protocol defined by a ZIP, there is sometimes a need to define an HD subtree that will not collide with keys derived for other protocols, as far as that is possible to assure by following the ZIP process 26.
Within this subtree, the application protocol may use derivation paths related to those used for existing key material — for example, to derive an account-level key. The following instantiation of the hardened key generation process may be used for this purpose.
It is strongly RECOMMENDED that implementors ensure that documentation of the context string(s), and the usage and derivation paths of the application protocol's key tree in the corresponding ZIP are substantially complete, before public deployment of software or hardware using this mechanism. The ZIP process allows for subsequent updates and corrections.
Let \(\mathsf{ContextString}\) be a globally-unique non-empty sequence of at most 252 bytes that identifies the desired context.
We instantiate the hardened key generation process with the following constants:
- \(\mathsf{Registered.MKGDomain} = \texttt{“ZIPRegistered\_KD”}\)
- \(\mathsf{Registered.CKDDomain} = \mathtt{0xAC}\)
Registered subtree root key generation 
Let \(S\) be a seed byte sequence meeting the requirements in Specification: Wallet seeds.
The registered subtree root is obtained as:
\(\mathsf{RegKD}(\mathsf{ContextString}, \mathsf{S}, \mathsf{ZipNumber})\) \(\rightarrow (\mathsf{sk}_{subtree}, \mathsf{c}_{subtree})\) :
- Let \((\mathsf{sk}_{m}, \mathsf{c}_{m}) = \mathsf{MKGh}^\mathsf{Registered}([\mathsf{length}(\mathsf{ContextString})]\,||\,\mathsf{ContextString}\,||\,[\mathsf{length}(S)]\,||\,S)\!\) .
- Return \(\mathsf{CKDh}^\mathsf{Registered}((\mathsf{sk}_{m}, \mathsf{c}_{m}), \mathsf{ZipNumber} + 2^{31}, 0, [\,])\!\) .
Note: The intermediate key \((\mathsf{sk}_{m}, \mathsf{c}_{m})\) would grant the ability to derive the subtree root for application protocols defined in any ZIP using the same \(\mathsf{ContextString}\) and seed. This is a potentially dangerous scope of grant since it cannot be known what future protocols will use this mechanism; therefore, \((\mathsf{sk}_{m}, \mathsf{c}_{m})\) SHOULD NOT be used or stored directly without careful consideration of security consequences.
Registered child key derivation 
As well as the integer child index \(i\!\) , the child key derivation function defined here supports a byte sequence \(\mathsf{tag}\!\) ; each pair \((i, \mathsf{tag})\) produces a different child key. If an explicit tag is not required, \(\mathsf{tag}\) is set to the empty byte sequence.
Note: The tag MUST use an unambiguous encoding within the given context. It is RECOMMENDED to use a prefix-free encoding, which may require the use of length fields if multiple fields need to be encoded.
\(\mathsf{CKDreg}((\mathsf{sk}_{par}, \mathsf{c}_{par}), i, \mathsf{tag})\) \(\rightarrow (\mathsf{sk}_{child}, \mathsf{c}_{child})\) :
- Return \(\mathsf{CKDh}^\mathsf{Registered}((\mathsf{sk}_{par}, \mathsf{c}_{par}), i, 0, \mathsf{tag})\!\) .
Full-width child cryptovalue derivation 
If the application protocol requires a 64-byte cryptovalue (for example, to avoid an entropy bottleneck in its subsequent operations), then a similar process to Registered child key derivation above can be used to obtain such a cryptovalue at a given child index; again with optional tag. The same considerations about encoding of the \(\mathsf{tag}\) apply as above.
\(\mathsf{derive\_child\_cryptovalue}((\mathsf{sk}_{par}, \mathsf{c}_{par}), i, \mathsf{tag})\) \(\rightarrow \mathsf{K}_{child}\) :
- Let \((I_L, I_R) = \mathsf{CKDh}^\mathsf{Registered}((\mathsf{sk}_{par}, \mathsf{c}_{par}), i, 1, \mathsf{tag})\!\) .
- Return \(I_L\,||\,I_R\!\) .
For the avoidance of doubt, the output of \(\mathsf{derive\_child\_cryptovalue}\) MUST NOT be provided as input to any key derivation function defined in ZIP 32. In particular, it MUST NOT be reinterpreted directly or indirectly as an input to \(\mathsf{CKDh}\!\) .
Specification: Ad-hoc key derivation (deprecated) 
For compatibility with existing deployments, we also define a mechanism to derive ad-hoc key trees for private use by applications, without ecosystem coordination. This was called "arbitrary key derivation" in previous iterations of this ZIP, but that term caused confusion as to the applicability of the mechanism.
Since there is no guarantee of non-collision between different application protocols, and no way to tie these key trees to well-defined specification or documentation processes, use of this mechanism is NOT RECOMMENDED for new protocols.
Let \(\mathsf{ContextString}\) be a globally-unique non-empty sequence of at most 252 bytes that identifies the desired context.
We instantiate the hardened key derivation process with the following constants:
- \(\mathsf{Adhoc.MKGDomain} = \texttt{“ZcashArbitraryKD”}\)
- \(\mathsf{Adhoc.CKDDomain} = \mathtt{0xAB}\)
Ad-hoc master key generation (deprecated) 
Let \(S\) be a seed byte sequence meeting the requirements in Specification: Wallet seeds.
The master extended ad-hoc key is:
\(m_\mathsf{Adhoc} = \mathsf{MKGh}^\mathsf{Adhoc}([\mathsf{length}(\mathsf{ContextString})]\,||\,\mathsf{ContextString}\,||\,[\mathsf{length}(S)]\,||\,S)\!\) .
Ad-hoc child key derivation (deprecated) 
\(\mathsf{CKDarb}((\mathsf{sk}_{par}, \mathsf{c}_{par}), i)\) \(\rightarrow (\mathsf{sk}_i, \mathsf{c}_i)\) :
- Return \(\mathsf{CKDh}^\mathsf{Adhoc}((\mathsf{sk}_{par}, \mathsf{c}_{par}), i, 0, [\,])\!\) .
Note: a previous iteration of this ZIP suggested that, if \(i\) is the last element of an HD path (i.e. no extension of this path is used), then the concatenation \(\mathsf{sk}_i\,||\,\mathsf{c}_i\) could be used as a 64-bit key. This is NOT RECOMMENDED, because it is difficult to define safe APIs that enforce the restriction that a given node in the key tree must not be used both in this way and to derive further child keys. Full-width child cryptovalue derivation provides a safe way to obtain the same functionality for new application protocols.
Specification: Wallet usage 
Existing Zcash-supporting HD wallets all use BIP 44 6 to organize their derived keys. In order to more easily mesh with existing user experiences, we broadly follow BIP 44's design here. However, we have altered the design where it makes sense to leverage features of shielded addresses.
Key path levels 
Sapling and Orchard key paths have the following three path levels at the top, all of which use hardened derivation:
- \(purpose\!\) : a constant set to \(32'\) (or \(\mathtt{0x80000020}\!\) ) following the BIP 43 recommendation. It indicates that the subtree of this node is used according to this specification.
- \(coin\_type\!\) : a constant identifying the cryptocurrency that this subtree's keys are used with. For compatibility with existing BIP 44 implementations, we use the same constants as defined in SLIP 44 7. Note that in keeping with that document, all cryptocurrency testnets share \(coin\_type\) index \(1\!\) .
- \(account\!\) : numbered from index \(0\) in sequentially increasing manner. Defined as in BIP 44 6.
Unlike BIP 44, none of the shielded key paths have a \(change\) path level. The use of change addresses in Bitcoin is a (failed) attempt to increase the difficulty of tracking users on the transaction graph, by segregating external and internal address usage. Shielded addresses are never publicly visible in transactions, which means that sending change back to the originating address is indistinguishable from using a change address.
Sapling key path 
Sapling provides a mechanism to allow the efficient creation of diversified payment addresses with the same spending authority. A group of such addresses shares the same full viewing key and incoming viewing key, and so creating as many unlinkable addresses as needed does not increase the cost of scanning the block chain for relevant transactions.
The above key path levels include an account identifier, which in all user interfaces is represented as a "bucket of funds" under the control of a single spending authority. Therefore, wallets implementing Sapling ZIP 32 derivation MUST support the following path for any account in range \(\{ 0\,..\, 2^{31} - 1 \}\!\) :
- \(m_\mathsf{Sapling} / purpose' / coin\_type' / account'\!\) .
Furthermore, wallets MUST support generating the default payment address (corresponding to the default diversifier as defined above) for any account they support. They MAY also support generating a stream of payment addresses for a given account, if they wish to maintain the user experience of giving a unique address to each recipient.
Note that a given account can have a maximum of approximately \(2^{87}\) payment addresses, because each diversifier has around a 50% chance of being invalid.
If in certain circumstances a wallet needs to derive independent spend authorities within a single account, they MAY additionally support a non-hardened \(address\_index\) path level as in 6:
- \(m_\mathsf{Sapling} / purpose' / coin\_type' / account' / address\_index\!\) .
zcashd version 4.6.0 and later uses this to derive "legacy" Sapling addresses from a mnemonic seed phrase under account \(\mathtt{0x7FFFFFFF}\!\) , using hardened derivation for \(address\_index\!\) .
Orchard key path 
Orchard supports diversified addresses with the same spending authority (like Sapling). A group of such addresses shares the same full viewing key and incoming viewing key, and so creating as many unlinkable addresses as needed does not increase the cost of scanning the block chain for relevant transactions.
The above key path levels include an account identifier, which in all user interfaces is represented as a "bucket of funds" under the control of a single spending authority. Therefore, wallets implementing Orchard ZIP 32 derivation MUST support the following path for any account in range \(\{ 0\,..\, 2^{31} - 1 \}\!\) :
- \(m_\mathsf{Orchard} / purpose' / coin\_type' / account'\!\) .
Furthermore, wallets MUST support generating the default payment address (corresponding to the default diversifier for Orchard) for any account they support. They MAY also support generating a stream of diversified payment addresses for a given account, if they wish to enable users to give a unique address to each recipient.
Note that a given account can have a maximum of \(2^{88}\) payment addresses (unlike Sapling, all Orchard diversifiers are valid).
Specification: Key Encodings 
The following encodings are analogous to the xprv and xpub encodings defined in BIP 32 for transparent keys and addresses. Each key type has a raw representation and a Bech32 8 encoding.
Sapling extended spending keys 
A Sapling extended spending key \((\mathsf{ask, nsk, ovk, dk, c})\!\) , at depth \(depth\!\) , with parent full viewing key tag \(parent\_fvk\_tag\) and child number \(i\!\) , is represented as a byte sequence:
- \(\mathsf{I2LEOSP}_{8}(depth)\) \(||\,parent\_fvk\_tag\) \(||\,\mathsf{I2LEOSP}_{32}(i)\) \(||\,\mathsf{c}\) \(||\,\mathsf{EncodeExtSKParts}(\mathsf{ask, nsk, ovk, dk})\!\) .
For the master extended spending key, \(depth\) is \(0\!\) , \(parent\_fvk\_tag\) is 4 zero bytes, and \(i\) is \(0\!\) .
When encoded as Bech32, the Human-Readable Part is secret-extended-key-main for the production network, or secret-extended-key-test for the test network.
Sapling extended full viewing keys 
A Sapling extended full viewing key \((\mathsf{ak, nk, ovk, dk, c})\!\) , at depth \(depth\!\) , with parent full viewing key tag \(parent\_fvk\_tag\) and child number \(i\!\) , is represented as a byte sequence:
- \(\mathsf{I2LEOSP}_{8}(depth)\) \(||\,parent\_fvk\_tag\) \(||\,\mathsf{I2LEOSP}_{32}(i)\) \(||\,\mathsf{c}\) \(||\,\mathsf{EncodeExtFVKParts}(\mathsf{ak, nk, ovk, dk})\!\) .
For the master extended full viewing key, \(depth\) is \(0\!\) , \(parent\_fvk\_tag\) is 4 zero bytes, and \(i\) is \(0\!\) .
When encoded as Bech32, the Human-Readable Part is zxviews for the production network, or zxviewtestsapling for the test network.
Orchard extended spending keys 
An Orchard extended spending key \((\mathsf{sk, c})\!\) , at depth \(depth\!\) , with parent full viewing key tag \(parent\_fvk\_tag\) and child number \(i\!\) , is represented as a byte sequence:
- \(\mathsf{I2LEOSP}_{8}(depth)\,||\,parent\_fvk\_tag\,||\,\mathsf{I2LEOSP}_{32}(i)\,||\,\mathsf{c}\,||\,\mathsf{sk}\!\) .
For the master extended spending key, \(depth\) is \(0\!\) , \(parent\_fvk\_tag\) is 4 zero bytes, and \(i\) is \(0\!\) .
When encoded as Bech32, the Human-Readable Part is secret-orchard-extsk-main for Mainnet, or secret-orchard-extsk-test for Testnet.
We define this encoding for completeness, however given that it includes the capability to derive child spending keys, we expect that most wallets will only expose the regular Orchard spending key encoding to users 21.
Values reserved due to previous specification for Sprout 
The following values were previously used in the specification of hierarchical derivation for Sprout, and therefore SHOULD NOT be used in future Zcash-related specifications:
- the \(\mathsf{BLAKE2b}\text{-}\mathsf{512}\) personalization \(\texttt{“ZcashIP32\_Sprout”}\!\) , formerly specified for derivation of the master key of the Sprout tree;
- the \(\mathsf{BLAKE2b}\text{-}\mathsf{256}\) personalization \(\texttt{“Zcash\_Sprout\_AFP”}\!\) , formerly specified for generation of Sprout address fingerprints;
- the \(\mathsf{PRF^{expand}}\) prefix \(\mathtt{0x80}\!\) , formerly specified for Sprout child key derivation;
- the Bech32 Human-Readable Parts
zxsproutandzxtestsprout, formerly specified for Sprout extended spending keys on Mainnet and Testnet respectively.
Test Vectors 
Test vectors are available at <https://github.com/zcash/zcash-test-vectors> in the sapling_zip32, sapling_zip32_hard, orchard_zip32, zip_0032_registered, and zip_0032_arbitrary files for each format.
Reference Implementation 
References 
| 1 | Information on BCP 14 — "RFC 2119: Key words for use in RFCs to Indicate Requirement Levels" and "RFC 8174: Ambiguity of Uppercase vs Lowercase in RFC 2119 Key Words" |
|---|
| 2 | BIP 32: Hierarchical Deterministic Wallets |
|---|
| 3 | BIP 39: Mnemonic code for generating deterministic keys |
|---|
| 4 | SLIP 39: Shamir's Secret-Sharing for Mnemonic Codes |
|---|
| 5 | BIP 43: Purpose Field for Deterministic Wallets |
|---|
| 6 | BIP 44: Multi-Account Hierarchy for Deterministic Wallets |
|---|
| 7 | SLIP 44: Registered coin types for BIP-0044 |
|---|
| 8 | BIP 173: Base32 address format for native v0-16 witness outputs |
|---|
| 9 | Zcash Protocol Specification, Version 2022.2.19 or later [NU5 proposal] |
|---|
| 10 | Zcash Protocol Specification, Version 2022.2.19. Section 3.12: Mainnet and Testnet |
|---|
| 11 | Zcash Protocol Specification, Version 2022.2.19. Section 4.2.2: Sapling Key Components |
|---|
| 12 | Zcash Protocol Specification, Version 2022.2.19. Section 4.2.3: Orchard Key Components |
|---|
| 13 | Zcash Protocol Specification, Version 2022.2.19. Section 5.4.1.6: DiversifyHash^Sapling and DiversifyHash^Orchard Hash Functions |
|---|
| 14 | Zcash Protocol Specification, Version 2022.2.19. Section 5.4.6.1: Spend Authorization Signature |
|---|
| 15 | Zcash Protocol Specification, Version 2022.2.19. Section 5.4.9.3: Jubjub |
|---|
| 16 | Zcash Protocol Specification, Version 2022.2.19. Section 5.6.2.1: Sprout Payment Addresses |
|---|
| 17 | Zcash Protocol Specification, Version 2022.2.19. Section 5.6.2.3: Sprout Spending Keys |
|---|
| 18 | Zcash Protocol Specification, Version 2022.2.19. Section 5.6.3.3: Sapling Full Viewing Keys |
|---|
| 19 | Zcash Protocol Specification, Version 2022.2.19. Section 5.6.3.4: Sapling Spending Keys |
|---|
| 20 | Zcash Protocol Specification, Version 2022.2.19. Section 5.6.4.4: Orchard Raw Full Viewing Keys |
|---|
| 21 | Zcash Protocol Specification, Version 2022.2.19. Section 5.6.4.5: Orchard Spending Keys |
|---|
| 22 | NIST Special Publication 800-38G — Recommendation for Block Cipher Modes of Operation: Methods for Format-Preserving Encryption |
|---|
| 23 | Understanding the Security of Zcash. Presentation by Daira-Emma Hopwood at Zcon3 (slides). |
|---|
| 24 | Understanding brute force. Daniel Bernstein, 2005. |
|---|
| 25 | Hybrid Encryption in the Multi-User Setting. Gregory M. Zaverucha, 2012. |
|---|
| 26 | ZIP 0: ZIP Process |
|---|
| 27 | ZIP 315: Best Practices for Wallet Implementations — Specification: Wallet seeds |
|---|
| 28 | ZIP 316: Unified Addresses and Unified Viewing Keys |
|---|
| 29 | ZIP 2005: Orchard Quantum Recoverability |
|---|